Negotiating with Ransomware Actors: Lessons from a Real Babuk Case
What a real-world ransomware negotiation reveals about leverage, governance gaps, and executive decision-making under pressure.
Key Takeaways
- Ransomware negotiation is a financial risk event, not a technical discussion.
- Attackers anchor high and use regulatory pressure as leverage.
- Most mid-market firms lack structured negotiation readiness.
- Governance maturity directly reduces ransom leverage.
The Incident
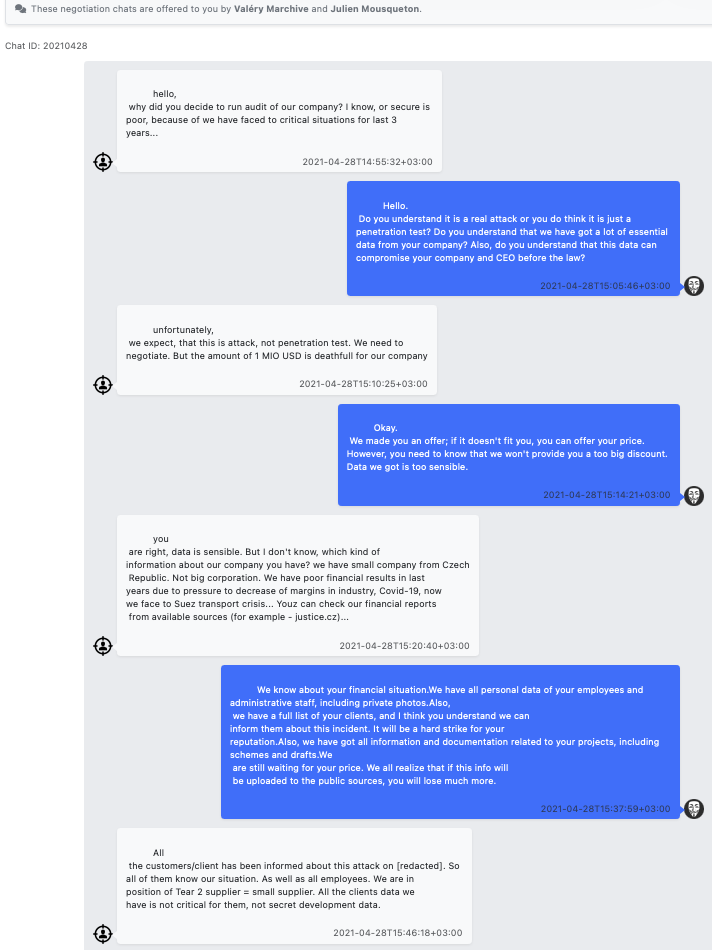
In April 2021, a small European manufacturing supplier fell victim to Babuk ransomware. The attackers demanded $1 million USD in cryptocurrency. Within hours, they offered a “50% discount” to $500,000 if payment was made within 72 hours.
The supplier operated with legacy Windows infrastructure, minimal segmentation, and no formal incident response plan. The attackers encrypted critical engineering data and exfiltrated customer information subject to GDPR regulations.
Throughout the negotiation, the threat actors emphasized their “reputation” for providing working decryption keys. They leveraged regulatory deadlines, implied reputational damage, and offered staged payment options. No enforceable guarantee existed beyond criminal goodwill.
What This Reveals About Modern Extortion
Psychological anchoring
The initial $1M demand was never realistic. It established a reference point that made $500K seem reasonable, even though both amounts were arbitrary.
Regulatory weaponization
GDPR notification requirements became a negotiation tool. The attackers understood compliance timelines better than the victim's leadership.
Executive alignment pressure
The negotiation exposed internal disagreements about authority, insurance coverage, and legal obligations. The attackers waited for internal consensus to break down.
Reputation as false assurance
Criminal trust is not enforceable. Paying does not guarantee data deletion, working decryption, or future immunity.
Small companies are soft targets
Mid-market firms have revenue but lack enterprise-grade security operations. They are more likely to pay and less likely to involve law enforcement.
The Executive Reality of Negotiation
Pay in Full
- Immediate decryption attempt
- No operational recovery guarantee
- Sets precedent for future targeting
- Legal and regulatory exposure persists
Negotiate
- Requires executive authority and legal counsel
- Buys time for parallel recovery
- Risk of escalation or data release
- No enforceable terms
Delay & Rebuild
- Extended downtime and revenue impact
- Data may be published or sold
- Requires functional backups
- Demonstrates resilience posture
Refuse & Prepare for Release
- Customer notification required
- Regulatory fines likely
- Reputational damage
- Eliminates future leverage
Where Governance Fails Before the Attack
The Babuk incident revealed systemic governance failures that existed long before encryption began:
- No formal risk management program aligned to business operations
- No defined accountability for OT and IT infrastructure security
- No accurate asset inventory or network segmentation
- No tested incident response plan with executive decision-making authority
- Weak remote access controls for vendors and engineers
ISA/IEC 62443 governance frameworks explicitly address these gaps. Mature organizations have documented security requirements, defined zones and conduits, and established response procedures before an incident occurs. This maturity reduces attacker leverage by limiting operational impact and providing clear decision-making pathways.
The Financial Lens
Ransomware is not a cybersecurity problem. It is an EBITDA problem. Downtime, recovery costs, ransom payments, and regulatory fines all impact profitability. Insurance premiums increase after incidents. Valuation multiples compress when buyers see operational risk.
Board members ask how this happened and why controls failed. Private equity operating partners evaluate whether the portfolio company is a liability. Customers and suppliers question continuity assurance.
The financial impact extends beyond the immediate incident. Trust erosion, contract renegotiations, and customer churn follow poor crisis management. Preparation is the only reliable discount in ransomware economics.
Our Position
Ransomware negotiation is structured risk management, not a technical debate. It requires executive authority, legal review, and a parallel rebuild strategy. The goal is leverage reduction, not moral arguments about payment.
Organizations that maintain governance maturity, operational visibility, and tested response procedures enter negotiations with options. Those that defer security preparation enter negotiations with hope.
Related Insights
Executive Ransomware Readiness Review
Assess your negotiation posture, incident response maturity, and governance alignment before you are forced into a crisis decision.
Preparation is the only reliable discount in ransomware economics.